TLS/SSL Security Scan
The padlock in the browser is just the beginning. Our deep analysis of your HTTPS setup ensures the entire
conversation between your users and your server is locked down tight.
Why Your TLS/SSL Health Matters
A weak TLS/SSL configuration is a welcome mat for attackers. It can expose sensitive data like passwords and credit card numbers to Man-in-the-Middle (MITM) attacks, breaking the trust you've built with your users and failing compliance audits like PCI DSS.
Protect Sensitive Data
Encrypt every byte of communication to stop attackers from snatching customer credentials and private information.
Build User Trust
That padlock isn't just for show. A rock-solid configuration tells visitors your site is legitimate and that their connection is safe.
Go Beyond a Simple Padlock Check
We dig deep to give you a complete picture of your configuration's health.
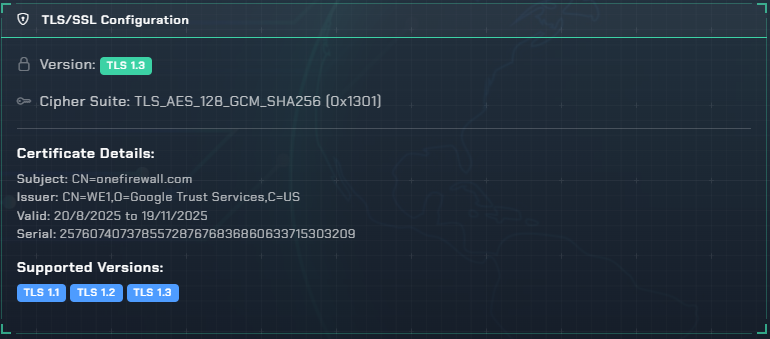
Certificate Validation
We verify the entire chain of trust, checking for expiration dates, hostname mismatches, and ensuring it's signed by a reputable authority. No more surprise certificate errors.
Protocol Support Analysis
Are you accidentally supporting legacy protocols? We flag outdated connections like SSLv3 and early TLS, which are vulnerable to nasty attacks like POODLE and BEAST.
Cipher Suite Strength
Not all encryption is created equal. We analyze your supported cipher suites, flagging weak algorithms (like RC4) and ensuring you're using modern, robust ciphers.
Common Vulnerabilities
We actively test for major vulnerabilities that have plagued the web, including Heartbleed, DROWN, and Logjam, giving you a clear pass/fail verdict for each.
HTTP Header Analysis
Security doesn't stop at the certificate. We check for crucial headers like HTTP Strict Transport Security (HSTS) that instruct browsers to enforce a secure connection.
Overall Security Grade
No need to be a cryptography expert. We distill all our findings into a simple A+ to F grade, so you know exactly where you stand and what to fix first.
Is Your Website's Connection Secure?
Guesswork isn't a security strategy. Stop wondering if your encryption is strong enough.
Run a free scan with vulnix0 and get an instant, actionable report.