Uncover Your Hidden Risks
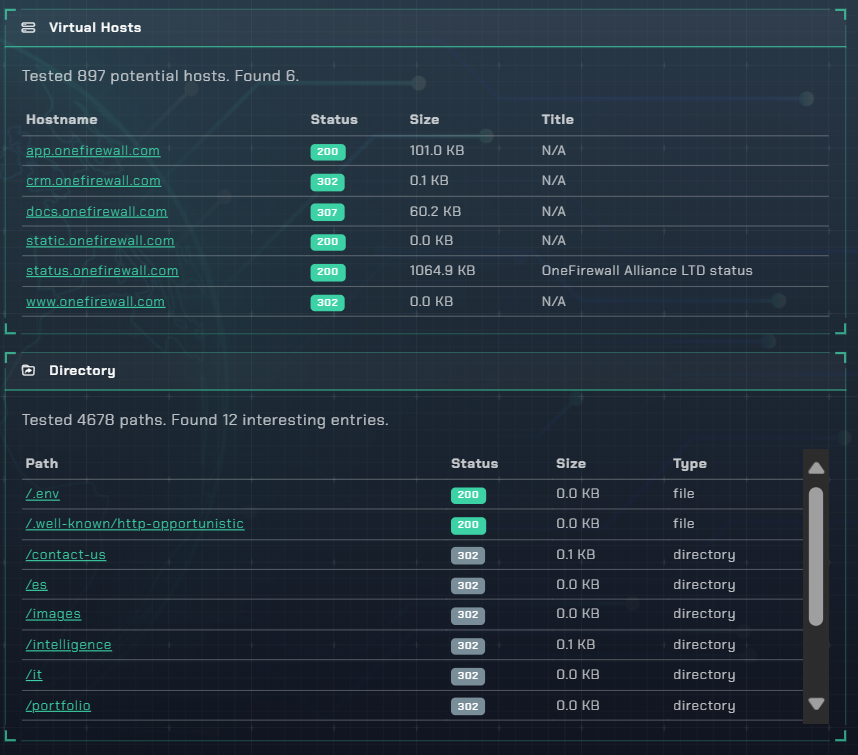
It's the forgotten files that cause the biggest breaches. Our discovery scanner relentlessly searches your web servers
for hidden backups, configs, and directories before an attacker does.
A Simple Mistake, A Devastating Breach
A single exposed file—a database backup, a config file with passwords, or an old log—is often all an attacker needs to take over your entire system. Our automated scan hardens your servers by making sure only public content is ever visible to the world.
Stop Leaking Your Secrets
Find exposed `.env` files or `wp-config.php` files that contain the keys to your kingdom—database passwords, API keys, and more.
Prevent Source Code Theft
Is your entire codebase public? We detect accessible `.git` directories and old backups (`.zip`, `.tar.gz`) that could leak your intellectual property.
The Critical Leaks We Hunt For
Our scanner uses an ever-growing list of thousands of patterns to find what others miss.
Exposed Config Files
We find those plain-text `.env` files and other configs that hand over your database passwords and API keys on a silver platter.
Forgotten Backups
That old database dump (`.sql`) or site backup (`.zip`, `.tar`) you forgot to delete? It’s a goldmine for attackers, and we’ll find it first.
Exposed `.git` Repository
A publicly exposed `.git` directory allows anyone to download your application's full source code and commit history. We flag it immediately.
Revealing Log Files
Log files can expose sensitive user data, internal network paths, and critical debug information. We find them before they're exploited.
Open Directories
When directory listing is on, anyone can browse your server's file structure like their own computer. We'll tell you where to shut the door.
Public API Docs
Exposed Swagger or OpenAPI docs can give attackers a complete roadmap to your internal APIs. We help you keep them under wraps.
Don't Let a Stray File Be Your Downfall
Run an automated discovery scan today and ensure your sensitive files stay private.
Secure Your Blind Spots