Uncover Hidden Risks in Your Live Applications
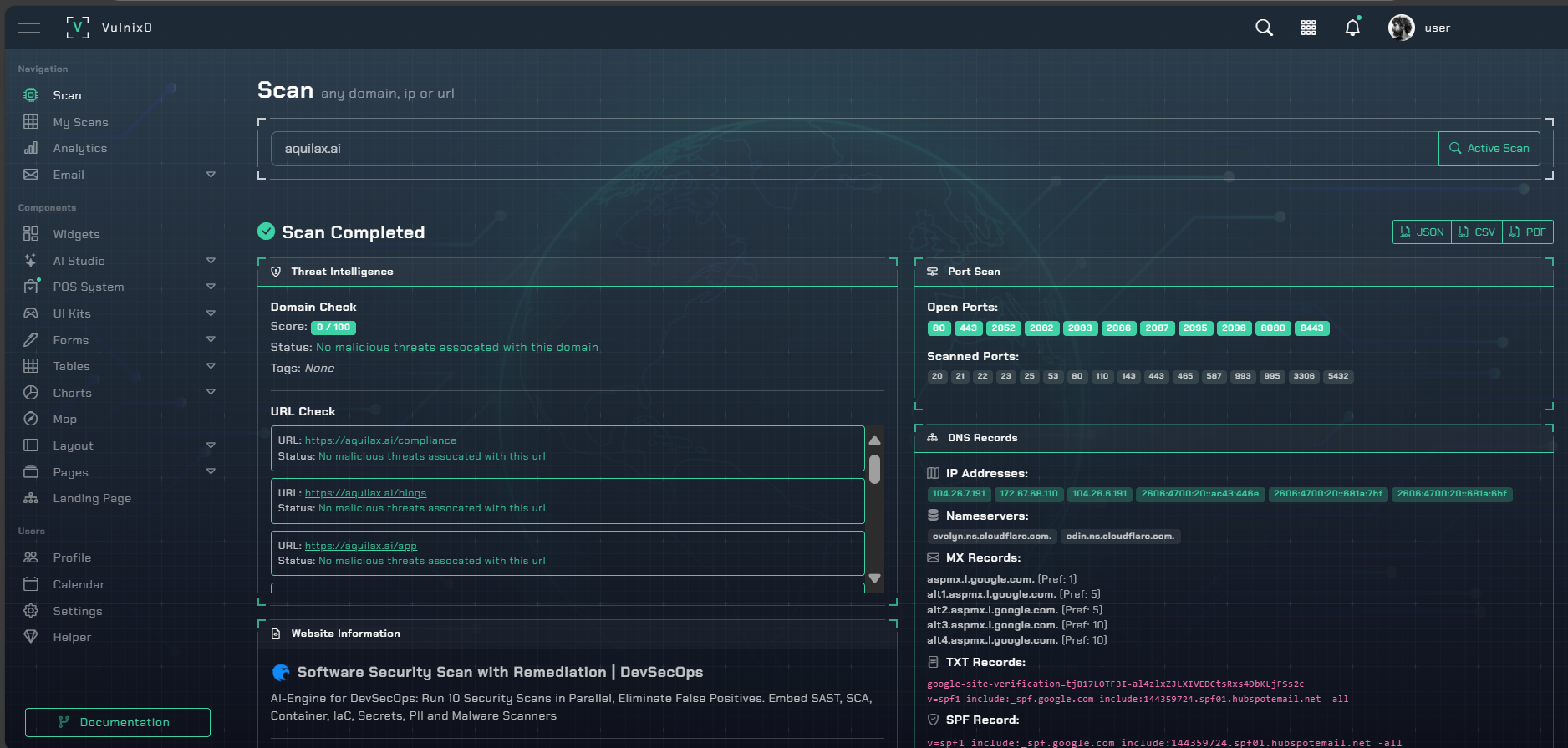
vulnix0's DAST scanner acts like a persistent, automated penetration tester, probing your running applications to find critical runtime vulnerabilities—like SQL Injection and Cross-Site Scripting (XSS)—without ever needing to see your source code.
By safely simulating real-world attacks, our DAST engine exposes flaws that only appear in a production-like environment. It's the essential final check for your CI/CD pipeline and the perfect tool for securing legacy systems and third-party components where code is unavailable.
Testing What Matters Most
Our DAST engine is finely tuned to discover high-impact vulnerabilities that attackers actively exploit.
OWASP Top 10 Coverage
Go beyond checklists. We provide deep testing for the most critical web risks like injections and broken authentication, giving you confidence in your security posture.
Modern API Security
Secure the backbone of your modern applications. We perform specialized tests for REST, GraphQL, and SOAP APIs to uncover endpoint vulnerabilities and prevent data breaches.
Authenticated Testing
Don't just test the login page. Our scanner intelligently navigates authentication flows to test the sensitive, user-only areas of your application for comprehensive coverage.
Built for Modern DevSecOps
Zero-Touch, Black-Box Scanning
Scan any web application or API, regardless of the underlying tech stack. No source code access required, making it perfect for any environment.
Intelligent Authenticated Scanning
Securely handles complex login sequences, session management, and single-page applications (SPAs) to thoroughly test protected areas.
Seamless CI/CD Integration
Integrate DAST scans directly into your build and release pipelines via API, catching critical vulnerabilities before they reach production.
Actionable Remediation Insights
Receive developer-friendly reports with detailed vulnerability evidence, including replicable HTTP requests, and clear guidance to accelerate remediation.