See Your Apps Through an Attacker's Eyes
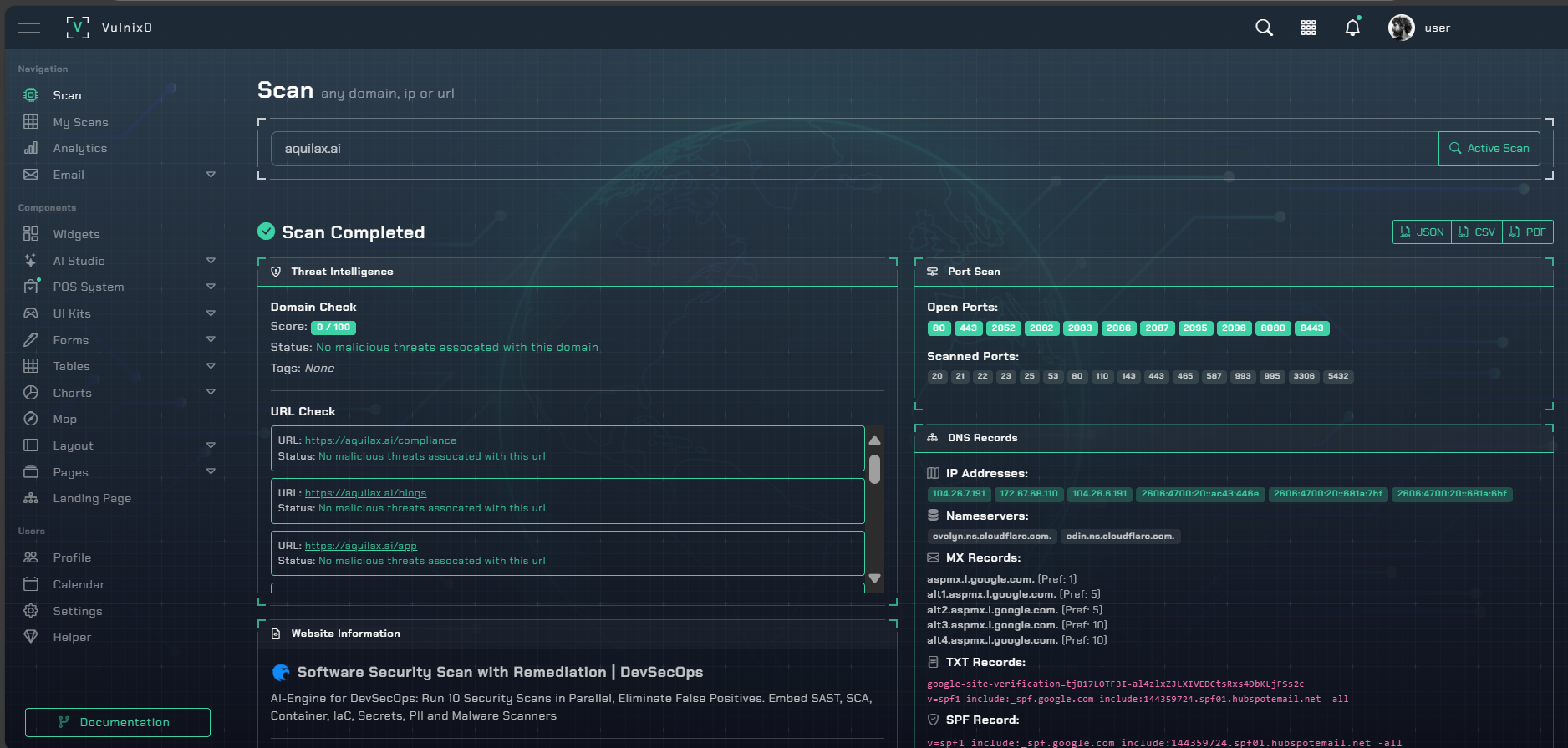
vulnix0’s DAST scanner shows you what a real attacker sees. It actively probes your running applications for runtime vulnerabilities like SQL Injection and Cross-Site Scripting (XSS), all without needing a single line of your source code.
By simulating real attack techniques, our DAST engine finds flaws that are invisible until your application is live. It’s the perfect way to secure legacy systems, vet third-party components, and integrate automated security testing right into your development pipeline.
A Focus on Real-World Risks
We find the critical vulnerabilities that attackers actively exploit in the wild.
OWASP Top 10 Coverage
We go straight for the jugular, testing for the most critical web security risks like injections, broken authentication, and security misconfigurations.
Modern API Security
Your APIs are your application's backbone. We provide specialized testing for REST, SOAP, and GraphQL to find vulnerabilities hidden deep within your services.
Authenticated Testing
What about areas behind a login? Our scanner authenticates just like a real user, letting it test for flaws in protected areas for deeper, more complete coverage.
Designed for Modern Security Workflows
Scan Any Tech Stack
It doesn't matter what your app is built with. Our black-box scanner tests from the outside in, just like an attacker would—no source code required.
Smart Authenticated Scanning
We intelligently handle complex login flows and maintain sessions to thoroughly test all the features and data accessible only to your authenticated users.
Automate Security in Your Pipeline
Easily integrate DAST scans into your CI/CD pipeline, empowering your team to find and fix vulnerabilities long before they ever reach production.
Clear, Actionable Fixes
We don't just find problems; we help you fix them. Every finding comes with developer-friendly guidance and the exact request/response to make remediation fast and simple.