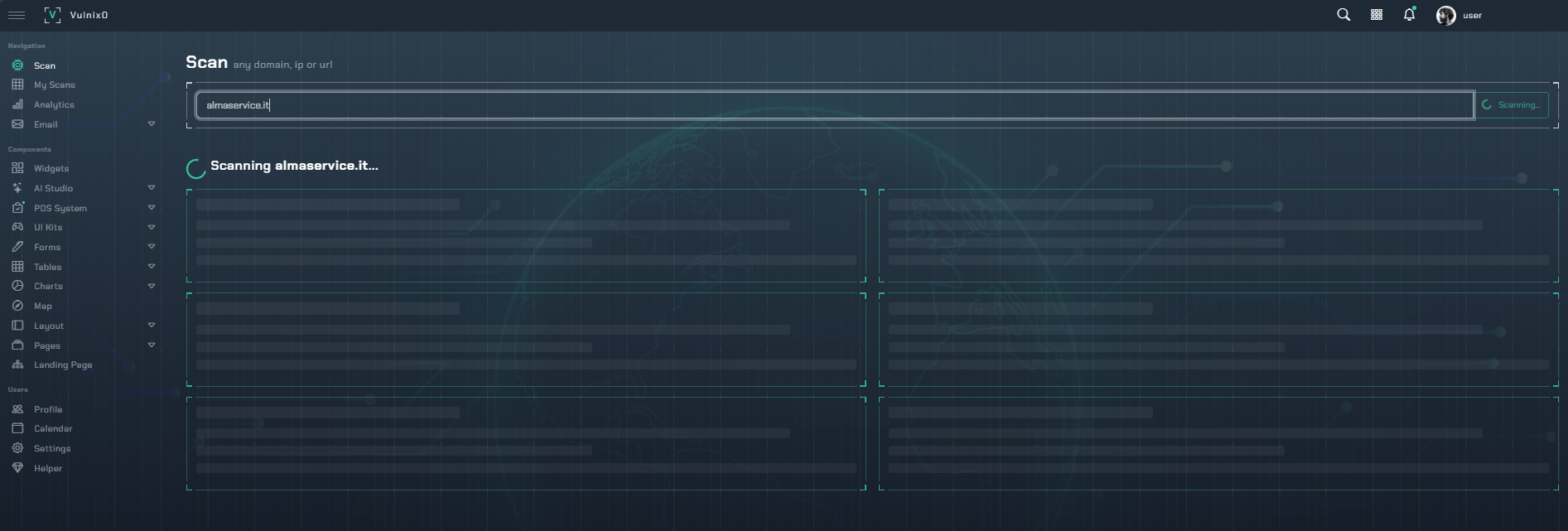
Automated Penetration Testing
Vulnerability scanners identify possibilities; our automated pentesting engine delivers certainty. By safely simulating real-world attack techniques, vulnix0 moves beyond theoretical risk to validate which vulnerabilities are truly exploitable, providing the proof you need to prioritize genuine threats.
From Potential Vulnerability to Validated Risk
Our validation process transforms scanner findings into confirmed, high-priority risks.
1. Safe Exploit Simulation
Leveraging a framework of safe, non-disruptive payloads, our engine mimics adversarial Tactics, Techniques, and Procedures (TTPs) to test for high-impact vulnerabilities.
2. Exploitability Validation
The engine confirms if a vulnerability is exploitable in your specific configuration, effectively eliminating false positives and freeing your team to focus on real threats.
3. Proof-of-Concept Generation
Every validated finding includes a detailed proof-of-concept (PoC) with replicable steps, empowering your teams to understand the risk and accelerate remediation.
Core Capabilities
Safe, Automated Exploitation
Our engine uses carefully crafted, non-disruptive payloads to safely confirm the exploitability of critical vulnerabilities (SQLi, RCE, XSS) without causing operational impact.
Attack Path Analysis
Our platform analyzes how multiple lower-risk vulnerabilities can be chained together to create a critical breach, revealing complex attack paths that scanners miss.
Industry Standard Methodologies
Testing is aligned with frameworks like the OWASP Top 10, ensuring systematic coverage of the most critical web application security risks.
Actionable Proof-of-Concept Reports
We generate clear reports with the concrete evidence needed for security and development teams to reproduce, understand, and rapidly remediate validated findings.